
“It’s beautiful” – Eight people experiencing homelessness to move into Pleasant Street apartments
Down every street in Dover, reminders of his late wife Stephanie followed Larry Regan. After she passed, he headed towards Concord to start anew. It’s taken a while for that to feel like a reality, but the day has finally come. For the last three...

Matt Fisk will serve as next principal of Bow High School
Assistant principals don’t typically serve students food, but at Bow High School, lunch duty is a daily responsibility for Matt Fisk.Last Wednesday, Fisk dished out Big Mac subs and cheese nachos and checked in with students as they passed through the...
Most Read
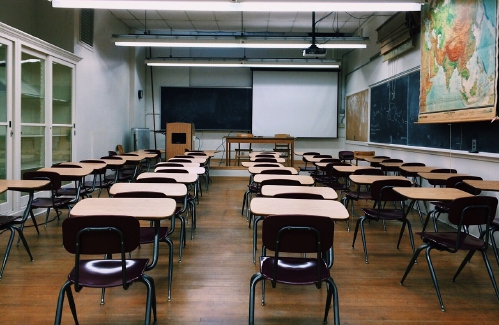
 N.H. Educators voice overwhelming concerns over State Board of Education’s proposals on minimum standards for public schools
N.H. Educators voice overwhelming concerns over State Board of Education’s proposals on minimum standards for public schools
 “It’s beautiful” – Eight people experiencing homelessness to move into Pleasant Street apartments
“It’s beautiful” – Eight people experiencing homelessness to move into Pleasant Street apartments
 Voice of the Pride: Merrimack Valley sophomore Nick Gelinas never misses a game
Voice of the Pride: Merrimack Valley sophomore Nick Gelinas never misses a game
 Matt Fisk will serve as next principal of Bow High School
Matt Fisk will serve as next principal of Bow High School
 Former Concord firefighter sues city, claiming years of homophobic sexual harassment, retaliation
Former Concord firefighter sues city, claiming years of homophobic sexual harassment, retaliation
 A trans teacher asked students about pronouns. Then the education commissioner found out.
A trans teacher asked students about pronouns. Then the education commissioner found out.
Editors Picks
 Concord martial arts studio builds life skills far beyond combat
Concord martial arts studio builds life skills far beyond combat
 Red barn on Warner Road near Concord/Hopkinton line to be preserved
Red barn on Warner Road near Concord/Hopkinton line to be preserved
 FAFSA fiasco hits New Hampshire college goers and universities hard
FAFSA fiasco hits New Hampshire college goers and universities hard
 Searchable Concord salary database: Top earners include more police, fewer women
Searchable Concord salary database: Top earners include more police, fewer women
Sports

High schools: Bow’s Kelly lifts Falcon softball to victory in walk-off, more Monday results, plus Saturday’s track meets
SoftballBow 5, Campbell 4Key players: Bow – Maddy Oppold (2-for-4), Ella Roos (3-for-4), Taylor Ouellette (2-for-4, 2 RBI), Emma Kelly (1-for-4, walk-off single), Lilly Wright (1-for-3, 2-run HR), Caly Poitras (4 IP, 7 H, 1 BB), Taylor Ouellette (3...
 Patriots’ draft approach likely to be different in post-Belichick era
Patriots’ draft approach likely to be different in post-Belichick era
 High schools: Weekend results
High schools: Weekend results
Opinion

Opinion: This stinks, but if you don’t speak up it’s going to reek
Celeste Clark is the executive director of Raymond Coalition For Youth. Think it’s not your issue so you don’t need to pay attention? Do you think, well I don’t use it so I really don’t care? Or, are you just plain sick of hearing about marijuana...
 Opinion: The problem with Ukraine
Opinion: The problem with Ukraine
 Opinion: This Earth Day, help keep local land clean and healthy
Opinion: This Earth Day, help keep local land clean and healthy
 Opinion: Adopting the right 306 Rules
Opinion: Adopting the right 306 Rules

Politics

Sununu says he’ll support Trump even if he’s convicted
As jury selection begins this week in the hush-money trial of former President Donald Trump, New Hampshire Gov. Chris Sununu says he doesn’t believe many voters view Trump’s criminal indictments, his actions on Jan. 6, 2021, or his election denialism...
 NH mayors want more help from state on homelessness prevention funds
NH mayors want more help from state on homelessness prevention funds
 Two democrats with parallel views run for same State Senate seat
Two democrats with parallel views run for same State Senate seat
 House passes bill removing exceptions to state voter ID law
House passes bill removing exceptions to state voter ID law
 League of Women Voters suing over AI robocalls sent in NH
League of Women Voters suing over AI robocalls sent in NH
Arts & Life

Community Players of Concord present newest adaptation of Pride and Prejudice
“Not Your Grandmother’s Jane Austen…”Bold, surprising, boisterous, and timely, this Pride and Prejudice for a new era explores the absurdities and thrills of finding your perfect (or imperfect) match in life.The outspoken Lizzy Bennet is determined to...
 Vintage Views: From darkness to light
Vintage Views: From darkness to light
 From the farm: Spring brings calves, beautiful calves
From the farm: Spring brings calves, beautiful calves
Obituaries
 Dennis Michael Schwab
Dennis Michael Schwab
Manchester, NH - It is with great sorrow that we announce the passing of Dennis Michael Schwab. He passed away on April 6th, 2024, after a period of failing health. He was 51 years old. With great dignity, Michael was very thankful to b... remainder of obit for Dennis Michael Schwab
 Jay T. Sweeney
Jay T. Sweeney
Lyman, ME - Jay T. Sweeney, 64, of Lyman Maine, Passed away unexpectedly on Tuesday, February 20, 2024. He was born in Concord, NH on October 13, 1959, son of John and Donna Cozzi, Sweeney. He graduated from Concord High school, Class ... remainder of obit for Jay T. Sweeney
 Patrick J. Pat" Lane
Patrick J. Pat" Lane
Patrick J. "Packin' Pat" Lane Concord , NH - Patrick Joseph Lane of Concord NH passed away suddenly in his home on April 8th. He was born in Seattle Washington October 8,1959. The son of Leo T. Lane and Blanche (Renshaw) Lane, the third... remainder of obit for Patrick J. Pat" Lane
 Lisa Marie Cheney
Lisa Marie Cheney
Lisa Marie (Jameson) Cheney Boscawen, NH - Lisa Marie (Jameson) Cheney, 56 of Boscawen NH, passed away peacefully April 17, 2024 at Granite VNA Hospice House with family by her side. Born in Concord, NH on April 20, 1967, Lisa was the da... remainder of obit for Lisa Marie Cheney
 Opinion: Inherited hatred and how to stop it
Opinion: Inherited hatred and how to stop it
 High schools: Coe-Brown softball wins 5th straight, Concord’s McDonald pitches first varsity win, Tide’s Doherty scores 100th career point
High schools: Coe-Brown softball wins 5th straight, Concord’s McDonald pitches first varsity win, Tide’s Doherty scores 100th career point
 At House hearing, some argue proposed transgender sports ban would violate discrimination law
At House hearing, some argue proposed transgender sports ban would violate discrimination law
 Committee approves bill allowing host communities to join charitable gaming
Committee approves bill allowing host communities to join charitable gaming
 Charities will not have to pay rent to casinos under new law
Charities will not have to pay rent to casinos under new law
 Upper Valley residents among advocates for NH aid-in-dying bill
Upper Valley residents among advocates for NH aid-in-dying bill
 Police: Man facing felony animal cruelty charge after striking, killing cat
Police: Man facing felony animal cruelty charge after striking, killing cat
 Affordable housing and child care remain top concerns for young people in N.H.
Affordable housing and child care remain top concerns for young people in N.H.
 N.H. legislators continue to ignore three-year-old school-funding recommendations
N.H. legislators continue to ignore three-year-old school-funding recommendations

 Gallery: Forty-mile gravel bicycle race draws racers from all over the region
Gallery: Forty-mile gravel bicycle race draws racers from all over the region Wednesday’s high schools: Fancher’s 2-run blast leads Concord baseball to victory; plus more baseball, softball, lax and tennis results
Wednesday’s high schools: Fancher’s 2-run blast leads Concord baseball to victory; plus more baseball, softball, lax and tennis results Opinion: Student power: Confronting collaborators and cowards at home and abroad
Opinion: Student power: Confronting collaborators and cowards at home and abroad Concord Monitor editor Mike Pride’s final book explores the lives, works of Northern New England poets
Concord Monitor editor Mike Pride’s final book explores the lives, works of Northern New England poets Active Aging: John Burke of Peterborough celebrated his 81st birthday with 81 hikes up Pack Monadnock
Active Aging: John Burke of Peterborough celebrated his 81st birthday with 81 hikes up Pack Monadnock
